Dear All,
I would like to check which service using a domain admin account and when did it authenticate and to which server it tried. For example I have SQL reporting server with Domain Admin. The service authenticates when it generates a reports.
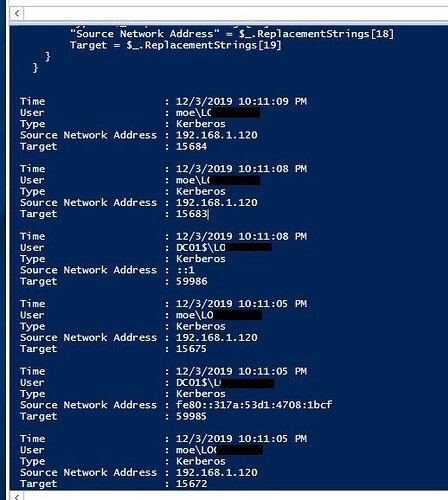
I would like to know on which server does this service works (IP of the server), Which user it uses, What kind of Authentication (Kerberos, Nego…etc) and if possible against which DC it authenticated.
I got this script below and it shows me these details (Source Network IP), User, Authentication Type, Date and Time. and this gets generated when the service restarts. The problem is that the script doesn’t bring the group members which I want only instead, it brings everything as you can in the screenshots.
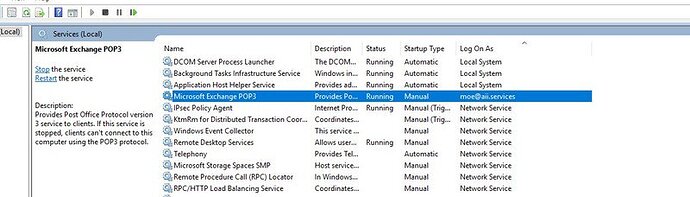
The below screenshots of Exchange Services, I have made a test by assigning the pop service a user called Moe. When running this script on AD (Dc01) it checks the logs and brings me all these details and the IP of Exchange Server (Where the service is running on) and the user its using.
I would appreciate if you could help me adjust the script to let it bring only domain admin users for instance.
Thank you
Get-EventLog -LogName Security -InstanceId 4624 | ForEach-Object { # translate the raw data into a new object [PSCustomObject]@{ Time = $_.TimeGenerated User = "{0}\{1}" -f $_.ReplacementStrings[5], $_.ReplacementStrings[6] Type = $_.ReplacementStrings[10] "Source Network Address" = $_.ReplacementStrings[18] Target = $_.ReplacementStrings[19] } }