Hi tbingeman,
Sorry for the long reply, but I think you’ll find some value in it…
I’m going to assume that you are looking to run a PowerShell script on a User’s system remotely… and while they (a non-admin) are logged in? From an IT standpoint, it’s best to login locally or remotely using your domain admin credentials to manage the system.
I’m not going to berate you about how the secure desktop (User Account Control) works because I can only assume you are very familiar with it. However, when it comes to scripting, it’s important to remember that all Elevated Permissions will go through the secure desktop for any program/process to truly be running with elevated permissions.
The easiest way to remember when a script might work is: No shield = No UAC, which in turn = no admin rights.
Your script is using a Run as different user method (no shield) and not Run as Administrator (shield).
Although you are using the -Credential switch and prepopulating the username - LocalAdmin - in your case, this only opens a credential request window - tied to the Credential Manager which is not an Admin feature. All of the Control Panel applets are in the system32 folder, so all will get you a UAC prompt… even when you’re logged in as an Admin (which I call a consent prompt yes/no).
I’ll share three examples that may help shine some light on why you can’t normally bypass the secure desktop to get elevated permissions:
I’m going to open three PowerShell sessions using three different methods:
- Standard User (no shield)
- Run as different user using local Administrator account (no shield; no UAC prompt)
- Run as Administrator (shield + UAC prompt)
I performed the following tasks in each PowerShell session in order:
Write-Host $env:USERPROFILE to show which profile is running that PowerShell session
- A standard user test account
- The built-in Administrator account
- The built-in Administrator account
Disabling a network adapter requires admin permissions. I tried disabling IPv6 on Ehternet0:
- Standard User got access is denied… as expected (no shield)
- Administrator got Access is denied… this is the Run as different user (no shield)
- Administrator was successful and verified results; this is the Run as Administrator session (shield)
The last test is opening Programs and Features using appwiz.cpl
- Standard User: opened successfully but gets a UAC prompt trying to uninstall a program
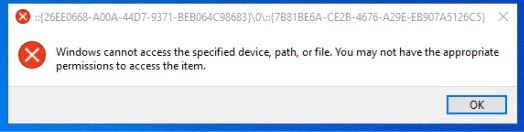
- Administrator: this one failed to open and throws up that same error you reported in your initial post
- Administrator: opened successfully but gets a UAC prompt trying to uninstall a program (expected)
I hope this helps shed some light on what you’re up against. I just don’t think there is a script that’s going to get you past the UAC without first modifying the UAC settings on all of the system in your organization…
The PLUS SIDE 
Login with your admin credentials and your scripts will make your job a lot easier… including the ones that need to run with elevated permissions. Then all you have to do is click Yes and let it run… while you take a coffee break!